Vulnerability management and compliance are two critical components of an effective cybersecurity strategy. Vulnerability management is the process of identifying, assessing, and mitigating vulnerabilities in systems and applications, while compliance refers to the adherence to regulatory and industry standards. Together, vulnerability management and compliance help organizations to protect against cyber threats, comply with regulations, and maintain the trust of customers and stakeholders.
Vulnerability management is essential for identifying and addressing vulnerabilities before they can be exploited by attackers. This proactive approach helps to reduce the risk of a data breach or other security incident, and can save organizations significant time and money.
Compliance, on the other hand, is essential for ensuring that organizations meet the requirements of regulatory and industry standards. This helps organizations to avoid penalties, fines, and sanctions, and maintain the trust of customers and stakeholders.
Implementing a vulnerability management program while navigating compliance frameworks can be challenging. Organizations often struggle to find the resources and expertise needed to effectively implement these processes. Additionally, compliance requirements can be complex and difficult to understand, making it challenging for organizations to ensure compliance.
Despite these challenges, vulnerability management is essential for protecting against cyber threats and maintaining compliance. By understanding the importance of vulnerability management, where it overlaps with compliance, and by implementing best practices and leveraging the latest technologies, organizations can effectively protect against cyber threats and comply with regulatory and industry standards.
The importance of vulnerability management
Vulnerability management is the process of identifying, assessing, and mitigating vulnerabilities in systems and applications. It is a critical component of an effective cybersecurity strategy, as it helps organizations to proactively identify and address vulnerabilities before they can be exploited by attackers.
One of the main reasons for the importance of vulnerability management is that it helps organizations to reduce the risk of a data breach or other security incident. By identifying and addressing vulnerabilities, organizations can reduce their attack surface and make it harder for attackers to exploit vulnerabilities. This can save organizations significant time and money, as the cost of a data breach can be significant.
Vulnerability management is also important for compliance. Many regulatory and industry standards, such as PCI DSS, HIPAA, NIST, ISO 27001, SOC2, FISMA, and GLBA, require organizations to implement vulnerability management practices. Organizations that fail to implement these practices can face penalties, fines, and sanctions.
Moreover, vulnerability management is important for protecting an organization’s reputation and maintaining the trust of customers and stakeholders. A data breach can have a significant impact on an organization’s reputation, and customers and stakeholders are increasingly concerned about the security of their personal data. By implementing vulnerability management, organizations can demonstrate their commitment to security and protect their reputation.
“80% of attacks use vulnerabilities reported three or more years ago”
– Check Point Security
Understanding the importance of vulnerability management is vital for organizations to protect against cyber threats, comply with regulatory and industry standards, and maintain the trust of customers and stakeholders. It is a proactive approach that helps to identify and address vulnerabilities before they can be exploited by attackers, reducing the risk of a security incident and the cost associated with it.
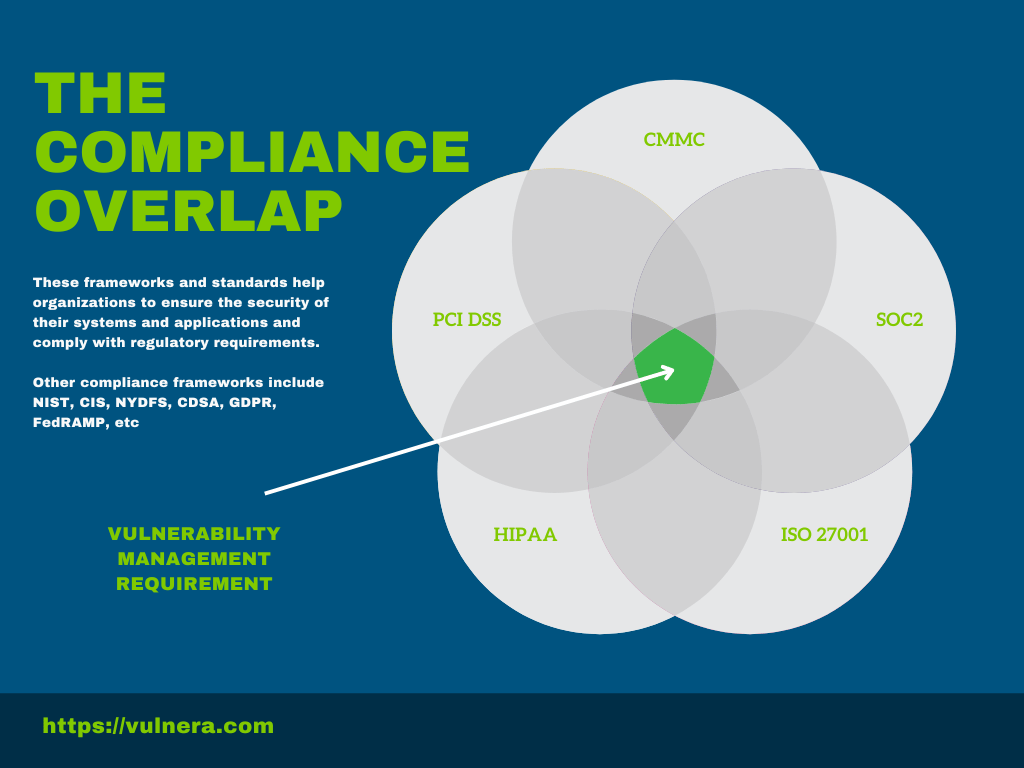
Common compliance frameworks and standards
There are several common compliance frameworks and standards that organizations must adhere to when implementing vulnerability management. These frameworks and standards help organizations to ensure the security of their systems and applications and comply with regulatory requirements.
One of the most commonly used frameworks for vulnerability management is the NIST Cybersecurity Framework (CSF). The NIST CSF provides a comprehensive framework for managing cybersecurity risk and includes guidelines for identifying and addressing vulnerabilities.
Another commonly used framework is ISO 27001. This international standard provides a framework for managing information security and includes specific requirements for vulnerability management, such as regular vulnerability assessments, incident response planning, and reporting on the status of vulnerabilities.
Another important framework is SOC2 (Service Organization Control 2), which is an auditing standard that organizations can use to demonstrate that they have implemented effective security controls, including vulnerability management.
“69% of MSPs report their clients struggle with compliance” – Kaseya
In addition to these frameworks, there are also several regulatory requirements that organizations must adhere to when implementing vulnerability management. For example, the Payment Card Industry Data Security Standard (PCI DSS) requires organizations that accept credit card payments to conduct regular vulnerability scans and penetration testing to identify vulnerabilities in their systems.
There are several common compliance frameworks and standards that organizations must adhere to when implementing vulnerability management. These frameworks and standards include NIST CSF, ISO 27001, SOC2, PCI DSS and many more. These frameworks and standards provide guidance on identifying and addressing vulnerabilities, incident response planning, and reporting on the status of vulnerabilities. Adhering to these frameworks and standards helps organizations to ensure the security of their systems and applications and comply with regulatory requirements.
Compliance requirements for vulnerability management
Compliance requirements for vulnerability management refer to the adherence to regulatory and industry standards that organizations must follow to ensure the security of their systems and applications. Many compliance frameworks, such as PCI DSS, HIPAA, NIST, ISO 27001, SOC2, FISMA, NYDFS, CMMC, and GLBA require organizations to implement vulnerability management practices.
For example, PCI DSS (Payment Card Industry Data Security Standard) requires organizations that accept credit card payments to conduct regular vulnerability scans and penetration testing to identify vulnerabilities in their systems. Similarly, HIPAA (Health Insurance Portability and Accountability Act) requires organizations in the healthcare industry to implement security measures to protect personal health information, including vulnerability management.
Compliance requirements for vulnerability management vary depending on the industry and the specific regulations that organizations must adhere to. However, in general, compliance requirements for vulnerability management include:
- Regular vulnerability assessments
- Remediation of identified vulnerabilities
- Reporting on the status of vulnerabilities
- Incident response planning
Additionally, compliance requirements for vulnerability management often require organizations to demonstrate that they have implemented a formal vulnerability management program, which includes policies, procedures, and standards for identifying and addressing vulnerabilities. Organizations that fail to comply with these requirements may face penalties, fines, and sanctions.
The challenges
Implementing vulnerability management for compliance can be challenging for organizations. Some of the common challenges include:
- Limited resources: Implementing vulnerability management can be resource-intensive, and organizations may not have the budget, staff, or expertise needed to implement the program.
- Limited visibility: Without proper visibility into the organization’s systems and applications, it can be difficult to identify vulnerabilities and potential attack vectors.
- Complexity: Compliance requirements can be complex and difficult to understand, making it challenging for organizations to ensure compliance.
- Difficulty in prioritizing vulnerabilities: With a large number of vulnerabilities to address, it can be difficult to prioritize and address the most critical vulnerabilities.
- Difficulty in demonstrating compliance: Organizations may struggle to demonstrate compliance with regulatory and industry standards, making it difficult to pass audits.
- Limited integration with other security controls: Vulnerability management may not be well-integrated with other security controls, such as incident response or threat intelligence, making it difficult to effectively mitigate vulnerabilities.
- Difficulty in keeping up with the latest threats: Vulnerability management can be difficult to keep up with the latest threats and vulnerabilities, making it difficult to protect against new attack methods.
- Difficulty in measuring the effectiveness of the program: Organizations may struggle to measure the effectiveness of their vulnerability management program, making it difficult to identify areas for improvement.
Implementing vulnerability management for compliance can be challenging for organizations. Limited resources, limited visibility, complexity, difficulty in prioritizing vulnerabilities, difficulty in demonstrating compliance, limited integration with other security controls, difficulty in keeping up with the latest threats and difficulty in measuring the effectiveness of the program are some of the common challenges that organizations face. Organizations need to address these challenges to ensure an effective vulnerability management program and compliance with regulatory and industry standards.
Best practices for integration
- Start with a risk assessment: Begin by conducting a risk assessment to identify the most critical vulnerabilities and compliance requirements. This will help organizations to prioritize their efforts and focus on the areas that are most critical to their business.
- Implement automation: Leverage automation to streamline vulnerability management and compliance processes. Automation can help organizations to identify and address vulnerabilities more quickly and efficiently.
- Establish a formal vulnerability management program: Implement a formal vulnerability management program that includes policies, procedures, and standards for identifying and addressing vulnerabilities. This will help organizations to ensure compliance with regulatory and industry standards.
- Regularly assess vulnerabilities: Regularly assess vulnerabilities to ensure that all systems and applications are secure and compliant. This will help organizations to identify new vulnerabilities and address them before they can be exploited by attackers.
- Integrate with other security controls: Integrate vulnerability management with other security controls, such as incident response and threat intelligence, to effectively mitigate vulnerabilities.
- Regularly report on the status of vulnerabilities: Regularly report on the status of vulnerabilities to demonstrate compliance and provide visibility into the organization’s security posture.
- Provide regular training and education: Provide regular training and education for staff to help them understand and appreciate the importance of vulnerability management and compliance.
Best practices for integrating vulnerability management and compliance include conducting a risk assessment, implementing automation, establishing a formal vulnerability management program, regularly assessing vulnerabilities, integrating with other security controls, regularly reporting on the status of vulnerabilities, and providing regular training and education. By following these best practices, organizations can effectively protect against cyber threats and maintain compliance with regulatory and industry standards.
The role of automation
- Automated vulnerability scanning: Automated vulnerability scanning can help organizations to identify vulnerabilities more quickly and efficiently than manual methods. Automated scanning tools can scan systems and applications on a regular basis, providing organizations with up-to-date information on vulnerabilities.
- Automated remediation: Automated remediation can help organizations to address vulnerabilities more quickly and efficiently. Automated remediation tools can automatically apply patches and updates to vulnerabilities, reducing the risk of a security incident.
- Automated reporting: Automated reporting can help organizations to demonstrate compliance with regulatory and industry standards. Automated reporting tools can generate regular reports on the status of vulnerabilities, providing organizations with visibility into their security posture.
- Automated compliance monitoring: Automated compliance monitoring can help organizations to ensure compliance with regulatory and industry standards. Automated compliance monitoring tools can automatically check systems and applications for compliance with specific requirements, providing organizations with real-time visibility into their compliance status.
- Automated incident response: Automated incident response can help organizations to respond to security incidents more quickly and efficiently. Automated incident response tools can automatically detect and respond to security incidents, reducing the risk of a security incident.
Automation plays a critical role in vulnerability management and compliance. Automated vulnerability scanning, automated remediation, automated reporting, automated compliance monitoring, and automated incident response can help organizations to identify and address vulnerabilities more quickly and efficiently, streamline processes, and improve compliance. Automation can also help organizations to demonstrate compliance with regulatory and industry standards, providing them with real-time visibility into their compliance status.
Looking into the future
- Cloud computing and IoT: The increasing adoption of cloud computing and the Internet of Things (IoT) will have a significant impact on vulnerability management and compliance. Organizations will need to ensure that their vulnerability management and compliance strategies are appropriate for these new environments.
- Automation: Automation will continue to play a critical role in vulnerability management and compliance. Organizations will need to automate their vulnerability management and compliance processes to stay ahead of new threats and regulatory requirements.
- Cybersecurity regulations: The regulatory landscape will continue to evolve, and organizations will need to stay up-to-date with the latest regulatory requirements. Organizations will need to ensure that their vulnerability management and compliance strategies are appropriate for their industry and comply with the latest regulations.
The future of vulnerability management and compliance will be shaped by the rapid pace of technological change and the evolving threat landscape. Organizations will need to adapt their vulnerability management and compliance strategies to stay ahead of new threats and regulatory requirements, considering the impact of cloud computing and IoT, automating processes, staying up-to-date with the latest regulatory requirements and adopting a risk-based approach.
Conclusions and next steps
Vulnerability management and compliance are two critical components of an effective cybersecurity strategy. Together, they help organizations to protect against cyber threats, comply with regulations, and maintain the trust of customers and stakeholders. However, implementing both can be challenging. Organizations often struggle to find the resources and expertise needed to effectively build both vulnerability management and compliance programs. Additionally, compliance requirements can be complex and difficult to understand, making it challenging for organizations to ensure adherence to required standards.
Leveraging the latest technologies are essential for organizations to effectively protect against cyber threats and comply with regulatory and industry standards. Organizations should start with a risk assessment, implement automation, establish a formal vulnerability management program, regularly assess vulnerabilities, integrate with other security controls, regularly report on the status of vulnerabilities, and provide regular training and education.
For next steps, organizations should consider the following:
- Conduct a thorough assessment of their current vulnerability management and compliance program to identify any gaps and areas for improvement.
- Develop a strategic plan to address any identified gaps and improve their vulnerability management and compliance program.
- Regularly review and update their vulnerability management and compliance program to keep up with the latest threats and regulatory requirements.
- Invest in the necessary resources and technologies to support their vulnerability management and compliance program.
- Communicate the importance of vulnerability management and compliance to all stakeholders, including employees, customers and partners, to build trust and support for the program.
By following these steps, organizations can effectively protect against cyber threats, maintain compliance and build trust with their stakeholders.
Closing thoughts
Organizations need to stay up-to-date with the latest threats and regulatory requirements, and be aware of the challenges they may face when implementing these processes. By understanding and addressing these challenges, organizations can ensure the security of their systems and applications and maintain trust with their stakeholders.
Vulnerability management and compliance are essential for organizations to protect against cyber threats and maintain regulatory compliance. Vulnerability management involves identifying, assessing, and mitigating vulnerabilities in systems and applications, while compliance refers to adhering to regulatory and industry standards. Implementing these processes can be challenging, but by following best practices, leveraging automation and technology, and adopting a risk-based approach, organizations can effectively implement vulnerability management and compliance.



