Faced with a continuously growing number of security threats and vulnerabilities, security teams are inundated with long lists of security alerts. They are faced with hundreds – if not thousands or tens of thousands – of security alerts a day. This can create complex problems for organizations trying to manage these alerts.
For teams trying to keep up with investigating and patching vulnerabilities within the environment, alert fatigue is a real problem. Not everything can be patched or otherwise mitigated. And, critical issues may be overlooked due to the sheer volume of information.
And for companies already struggling to hire qualified cybersecurity resources, current employees are reporting feeling emotionally overwhelmed and burned out.
Fortunately, using a risk-based approach to managing vulnerabilities offers a better solution to the traditional scan, patch, and hope for the best. Prioritization of security alerts has become an important part of a mature vulnerability management program.
What is Risk Prioritization?
Determining which security risks should be actioned first is the crux of all security teams. It is not possible to address every vulnerability of the hundreds or thousands. So which vulnerabilities should be actioned first?
Risk prioritization answers this question by evaluating the likelihood of a risk being exploited and the impact that would have to the organization. Then those identified as most critical to the organization are the ones that should be actioned first.
How to Prioritize Risk
Let’s explore the process of categorizing and scoring the vulnerabilities that have been found.
-
Asset Insights
The first step in prioritizing risk within the organization is knowing which assets and services are connecting to your network, in real-time. You also must identify any vulnerabilities these assets introduce to the organization. You cannot manage what you do not know exists. These assets and services may be internal, external and within the cloud. And third-parties such as vendors and service providers may actually pose the most risk to your network.
A list of accessible assets, including hosts, hostnames, IPs, ports, and services, should be compiled. Then a deeper analysis of these live assets should be completed to identify security issues present including matching previously identified known issues as well as any insecure configurations.
-
Risk Scoring
Once vulnerabilities are identified, they are analyzed to determine the probability of a risk event occurring and the potential impact to the organization. They are often ranked on a numerical and/or color-coded scale from least to most critical.
To help understand and likelihood of impact that vulnerabilities bring to the organization, there are several resources available for obtaining information:
- Vulnerability Databases
- CERT (CISA) Advisories
- Vendors (Cisco, VMware, Apple, Microsoft, etc.)
- Criminal Forums and Dark Web Markets
CVSS vs. CVE vs. NVD
Some of the most commonly used risk-scoring resources used by security teams include:
Common Vulnerability Scoring System (CVSS)
CVSS is an open framework for scoring computer vulnerabilities between 0 and 10 for base, temporal, and environmental groups. More information on CVSS can be found at: www.first.org/cvss.
Common Vulnerability and Exposure (CVE)
CVE refers to a list of publicly disclosed cybersecurity weaknesses, organized by identification numbers with descriptions and published dates, which is maintained by the MITRE organization. It is very common for vulnerability reports to cross reference the vulnerabilities with the CVE id because different security organizations may describe a vulnerability differently, but they may all refer to the same CVE ID. More information can be found at http://cve.mitre.org/.
National Vulnerability Database (NVD)
NVD is a comprehensive cybersecurity vulnerability database that integrates all publicly available U.S. government vulnerability resources and provides references to industry resources. It is based on and synchronized with the CVE and provides a severity score using CVSS. More information can be found at http://nvd.nist.gov.
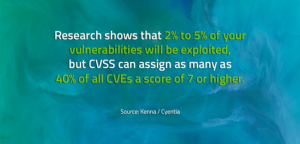
It is important to note that while CVEs and CVSS are useful in prioritizing risk, their value is limited. This is due to the dynamic nature of vulnerabilities and how they are exploited. They generally lack key information such as exploit codes, fixes, popular targets, known malware, remote code execution details, etc. In addition, these scores are static and based on the initial assessment of their potential to be exploited. They are rarely, if ever, updated. They are NOT designed to provide insight into the criticality of each vulnerability within a specific enterprise environment.
Basing patching on a CVSS score alone may end up wasting limited time and resources for remediation. Many vulnerabilities with high CVSS scores pose little or no risk of exploitation.
How VSCORE Makes a Difference
VULNERA recognized the limitations of these scoring tools and developed a proprietary tool known as VSCORE. The VSCORE helps teams automatically classify and prioritize threats found within the environment during the assessment phase. It considers multiple sources of threat intelligence as well as additional vulnerability criteria, including:
- Active exploits available on the internet or in exploit packs
- Are remotely exploitable
- Often result in arbitrary code execution
- Being used in known exploit campaigns
- Have active advisories from vendors and regulating bodies
Based on all these metrics, threats can be prioritized by calculating a single VSCORE. It provides a numeric and visual tool for communicating the level of risk to stakeholders and provides insight into where resources are needed to manage and mitigate high risk/critical threats. A recommended method of remediation is also provided.
Since the environment is being continuously assessed, information on the VULNERA dashboard is portrayed in real-time as the attack surface changes across the environment.
As a result, security teams can invest limited resources on those issues that demand the most attention and to maximize risk reduction. And, this additional layer of context surrounding the real risk of vulnerabilities helps curate, classify, and reduce the number of alerts.
Learn About VSCORE and Vulnerability Intelligence
For more information on VULNERA’s VSCORE Prioritization and Vulnerability Intelligence download one of our Solution Briefs by clicking the image below. You’ll get additional details including information displayed across the dashboards and how CISOs, tech, and compliance teams are using them to mature their vulnerability management programs.